By Lakshmanan
The Russia-linked threat actor known as APT29 targeted European diplomatic missions and Ministries of Foreign Affairs as part of a series of spear-phishing campaigns mounted in October and November 2021.
According to ESET’s T3 2021 Threat Report shared with The Hacker News, the intrusions paved the way for the deployment of Cobalt Strike Beacon on compromised systems, followed by leveraging the foothold to drop additional malware for gathering information about the hosts and other machines in the same network.
Also tracked under the names The Dukes, Cozy Bear, and Nobelium, the advanced persistent threat group is an infamous cyber-espionage group that has been active for more than a decade, with its attacks targeting Europe and the U.S., before it gained widespread attention for the supply‐chain compromise of SolarWinds, leading to further infections in several downstream entities, including U.S. government agencies in 2020.
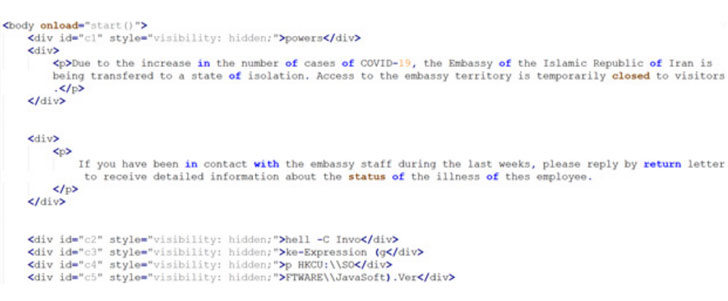
The spear-phishing attacks commenced with a COVID-19-themed phishing email impersonating the Iranian Ministry of Foreign Affairs and containing an HTML attachment that, when opened, prompts the recipients to open or save what appears to be an ISO disk image file (“Covid.iso”).
Should the victim opt to open or download the file, “a small piece of JavaScript decodes the ISO file, which is embedded directly in the HTML attachment.” The disk image file, in turn, includes an HTML application that’s executed using mshta.exe to run a piece of PowerShell code that ultimately loads the Cobalt Strike Beacon onto the infected system.
ESET also characterized APT29’s reliance on HTML and ISO disk images (or VHDX files) as an evasion technique orchestrated specifically to evade Mark of the Web (MOTW) protections, a security feature introduced by Microsoft to determine the origin of a file.
“An ISO disk image doesn’t propagate the so-called Mark of the Web to the files inside the disk image,” the researchers said. “As such, and even if the ISO were downloaded from the internet, no warning would be dis- played to the victim when the HTA is opened.”
Upon successfully gaining initial access, the threat actor delivered a variety of off-the-shelf tools to query the target’s Active Directory (AdFind), execute commands on a remote machine using SMB protocol (Sharp-SMBExec), carry out reconnaissance (SharpView), and even an exploit for a Windows privilege escalation flaw (CVE-2021-36934) to carry out follow-on attacks.
“Recent months have shown that The Dukes are a serious threat to western organizations, especially in the diplomatic sector,” the researchers noted. “They are very persistent, have good operational security, and they know how to create convincing phishing messages.”
Credit | The Hackers News

